Field Report: ” Phished by Association”
When it comes to phishing, attackers are becoming highly creative in the way they deliver the phish. They are doing a lot more reconnaissance work and it is our duty to ensure we are being more alert to avoid this form of social engineering.
SIGNS OF DANGER
Recently, Ostra came across a case of “phishing by association” that is a great reminder of why it is important for businesses to foster open and transparent relationships with vendors and partners.
One Friday evening, a client contacted us to say that she strongly believed her workstation had been compromised. After hearing her concerns, the Ostra Cybersecurity Defense Team started vigorously working on the situation.
We began with a few questions to get more information as to why she believed her environment had been compromised. She mentioned a vendor she was doing business with had been breached, and the cyber criminals sent phishing emails to their contacts. When she received the phishing email, she unfortunately clicked on it because she thought it was a legitimate email from the vendor.
CONTAINING THE THREAT
The first thing Ostra encouraged the client to do was to reset all her passwords. In situations like this, attackers are gathering credentials to hold for future use. Changing passwords immediately prevents the use of the credentials.
After ensuring the client changed her passwords, we immediately started reviewing her traffic logs to search for any suspicious events.
Fortunately, everything seemed healthy on her workstation and connected devices. However, Ostra continued to monitor the situation over the weekend and through the following week until we were satisfied that no damage had been done and her environment was secure.
Eunice Asemnor, Security Analyst at Ostra, stated that it was especially helpful that the client reached out immediately after clicking the email in this case. “It gave our Cyber Defense Team the ability to promptly remediate and handle the situation.” She added that this scenario illustrates the importance of being cautious with every email you receive—even from trusted vendors.
TAKEAWAYS FROM THE TRAIL
Although many phishing emails come from strangers, “phishing by association” is a tactic where cyber criminals send emails that appear to originate from a vendor that the client has worked with in the past.
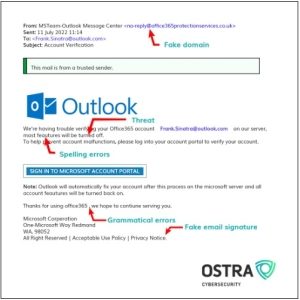
Shown above is an example of what this type of phishing email might look like, along with some clues that it warrants further scrutiny.
Even if a company has all the best cybersecurity measures in place, they can still be vulnerable to attacks if their third-party vendors are not protected. This is why Ostra encourages clients to build trust through proactive communication with outside vendors, while also holding them accountable to ensure they are keeping up with the best security practices.
5 Tips for Phishing Prevention
Ostra recommends taking the following steps to minimize your risk of falling victim to a phishing scheme:
- When using email, always be careful and take necessary precautions before clicking links or opening attachments.
- Watch for the following red flags, which are indications that the email could be a phishing attempt:
-
- Spelling mistakes, typos, unusual phrases or poor grammar.
- Calls to action that include deadlines or suggested consequences to create panic.
- Beware of bogus links. Like in the case of our client, phishing attempts may include a legitimate-looking link. Simply hover your mouse over the link and it will reveal the actual URL. Most trustworthy banks and financial institutions use “https://” in their URL. You can also search for the company’s official website, and then compare their domain to the URL being represented in the email.
- Be diligent in examining “From” addresses, which can be forged to appear legitimate. Attackers can use a minor typo to make it appear like it is coming from your CEO or bank. Be very alert to check if the email is coming from a true source.
- Emails requesting personal information should always be handled with care. Do not provide usernames, passwords, or other personal company information without due diligence.
NEED A CYBER GUIDE?
At Ostra, we pride ourselves on educating our clients and providing Fortune 100-caliber cybersecurity to businesses of every size—including small and medium-sized companies. To explore how you can get started with a trusted cybersecurity advisor to better protect your business or clients from phishing attempts, ransomware and other cyber threats, contact Ostra today.

Eunice Asemnor is a Security Analyst at Ostra Cybersecurity, a multi-layered and fully managed Security as a Service. With expertise in SIEM technologies, cybersecurity solutions, and advanced threat defense, Eunice plays a key role in protecting Ostra’s clients as a member of Your Trusted Cybersecurity Team.




