Cybersecurity 101: The Basics Of Keeping Your Business Secure (2021 Guide)
Cybersecurity can be an obscure and broad term covering everything from sophisticated digital systems to simple Norton anti-virus software. It’s important to know the nature of cyber threats and how you can protect your business against them.
Experts predict that cybercrime in 2021 will cost companies around the globe $6 trillion. By 2025, that number is expected to increase to $10.5 trillion. We have to treat cybersecurity protection as an essential part of business operations.
In this guide, we’ll be breaking down cybersecurity concepts and why it matters in 2021. With an increase in remote working and a rise in cyberattacks, protecting your sensitive data is more important than ever. Understanding the basics of cybersecurity is essential to protecting your business and keeping your data safe.
Regardless of industry – manufacturing, financial services, healthcare, etc.— sensitive data is at the core of business operations. This data can include credit card information, passwords, financial records, patient information, and more. Data breaches can cause a loss in profits, and even more severe, an irreparable break in consumers’ trust. While it is critically important to protect other people’s data, a business also needs to protect its own and ensure it can maintain operations (and reputation) and properly defend against a ransomware attack.
According to this Forbes article, in today’s digital age, every company is a data company, and with this data comes the responsibility of ensuring its safety. It’s our duty as business managers to protect our business operations, our data.
The Importance of Cybersecurity in 2021
This year COVID -19 has forced businesses to adapt their digital security measures as they navigate working remotely. Even after a vaccine becomes readily available, working from home is likely to continue indefinitely.
Businesses and employees have adjusted to remaining productive and carry out business-as-usual while working from home. But, remote workers connecting from personal devices and open networks open the door for an increase in cyberattacks.
The FBI recently reported that the number of complaints about cyberattacks to their Cyber Division went up to as many as 4,000 per day. This represents an astonishingly 400% increase from the complaints they saw pre-COVID.
Today, the question for many business owners is, how to adapt to remote working and still protect their business, clients, and data.
Cybercriminal Methods: What to Be on the Lookout For
In the mid-2000s, 80% of cybercriminals worked independently or were freelancers. They made up an unsophisticated and less skilled group of cyberattacks. As more data is exchanged online and technology has evolved, cybercriminals have gotten more sophisticated. Today, 80% of cybercrimes are part of an underground cybercrime organization and weave complicated and novel cyberattacks.
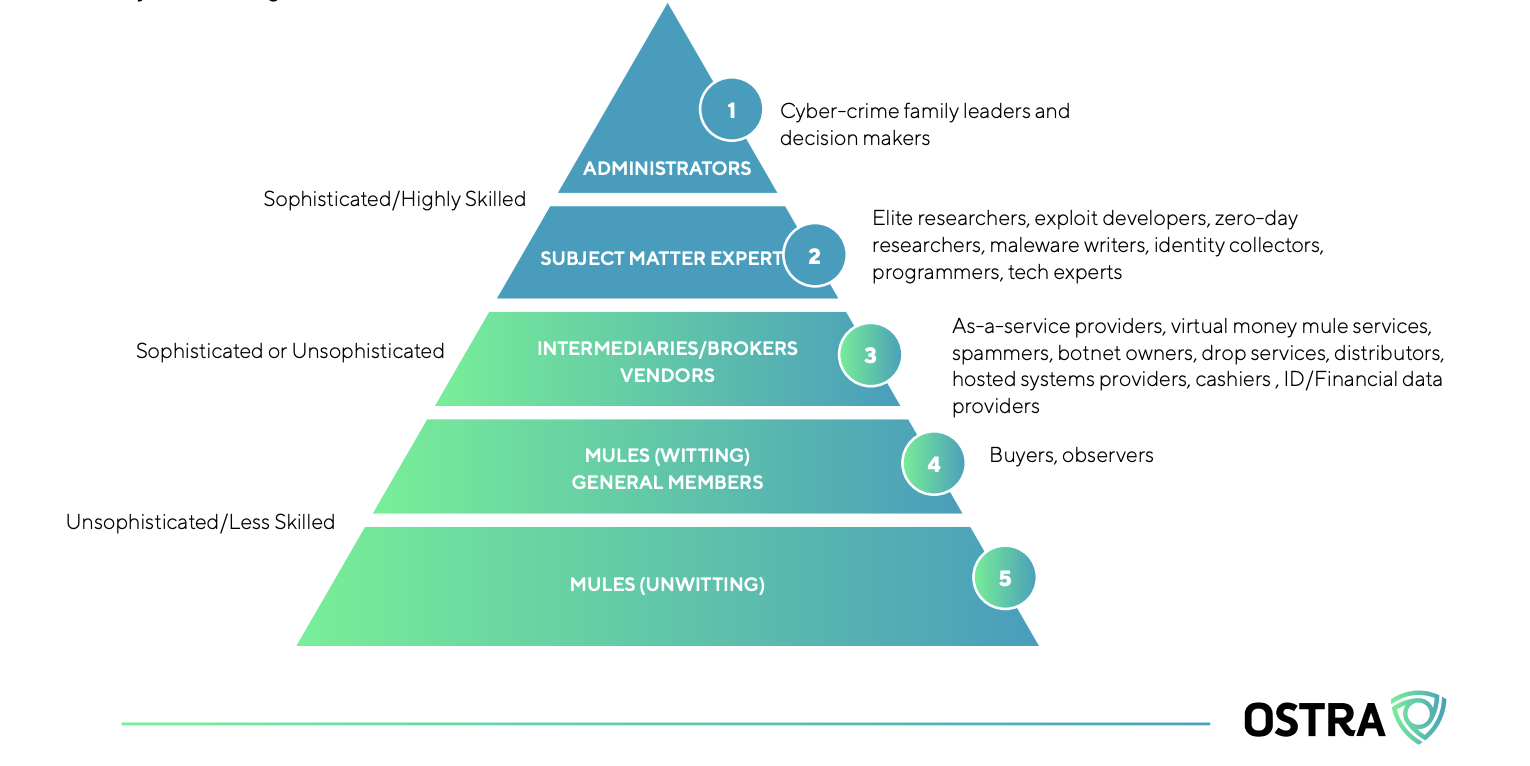
A pyramid outlining the levels of a cybercrime organization.
The methodology of cybercriminals has evolved over time. Initially, viruses had to be transferred through computer discs. Today, viruses can spread through the internet like wildfire.
Here are some of the key cybersecurity terms and ways in which cybercriminals will attempt to gain access to your company’s data:
Social Engineering and Phishing
Social engineering and phishing involve an attempt at getting personal information under the guise of a trusted source. For example, receiving an email from an email address that looks like your local bank’s email address saying they need you to confirm your account by providing personal information. The email address may also look like the company’s email, and the sender (cybercriminal) may request login credentials.
When an employee’s information is compromised, the hacker may try to bypass security perimeters, distribute malware inside a closed environment, or gain access to secured data.
How to Keep Phishing Threats at Bay:
- Implement two-factor authentication
- Enforce strict password requirements
- Educate employees about the dangers of phishing
Malware
Malware—or malicious software—is one of the most popular types of cybercrime. Able to exist in many different formats, it is a versatile method. It can take the form of a trojan virus, worms, or spyware and can be difficult to get rid of.
For an example of malware in action, let’s look at the trojan virus. An employee sees an ad online for an ad blocker. They download the blocker, which turns out to be a virus posing as helpful software. Once the virus has been downloaded, the hacker is free to wreak havoc by accessing sensitive data and then modifying, blocking, or deleting the data.
How to Stop Malware Attacks in Their Tracks:
- Secure your network through security solutions like firewalls
- Work with an experienced cybersecurity provider
- Install anti-virus software
Ransomware
Ransomware—a type of malware—is malicious software that locks up all the operating systems of a computer and displays a message demanding a fee to regain control of your system. Ransomware can be especially difficult to deal with, as you don’t want to pay the ransom. However, you also don’t want to have your system locked for too long, as this can endanger productivity for your business.
Ransomware can come in different forms, with phishing emails being one of the more popular vehicles. Say an employee opens up one of these emails and clicks on a link asking them to reset their password. Once they click the link, the ransomware downloads itself onto the computer and locks the user out. A pop-up message appears on the screen saying that they need to pay a ransom if they want to regain access. The company pays the ransom, and then they must go through their system and fix any issues and assess the damage. At this point, income has been lost due to these delays and any compromised data. In addition, the company loses credibility with its clients, suppliers, and other stakeholders.
How to Avoid Ransomware Attacks:
- Make sure all your software is up to date with patches
- Use reliable antivirus software and a firewall
- Backup all your files in the event an attack does occur
What Parts of Your Business to Protect

Here are some key areas of your business to ensure you are protected and how cybersecurity service providers like Ostra can help keep your data safe.
Keep Emails Safe
Email is one of the key mediums that cybercriminals use to commit their crimes. Ensure all your employees use a secure email service and don’t send work emails from their personal accounts. In addition, educate your employees about the importance of being vigilant while using their emails.
Ensure Mobile Devices Are Secure
Eighty-five percent of people use their smartphones to access their emails. That means it’s likely many of your employees do the same. Working with a qualified, experienced cybersecurity team is the best way to prevent mobile devices from being compromised, as they can leverage the latest mobile security solutions to keep your data safe.
Identify and Secure All Endpoints
Map out your network endpoints and use cybersecurity solutions to protect them. As we mentioned earlier, there are a multitude of avenues that cybercriminals can attempt to gain access into your system. Endpoints that businesses need to keep secure include desktops, laptops, smartphones, tablets, servers, workstations, internet-of-things devices, etc.
Utilize Cloud Security Solutions
Cloud security is a solution that every business should consider. In addition to being scalable, housing all your data in the cloud can be more secure than storing it on-premise. When looking for a cloud service provider, validate that they are investing heavily in security. By partnering with a cloud security provider like Ostra, you can ensure that as your business moves to the cloud your data is secure.
How Ostra Can Help Keep Your Data Secure and Safe
Are you feeling overwhelmed about the prospects of keeping all your data safe? Don’t worry, we’ve got your back.
Ostra offers a comprehensive cybersecurity solution that can be customized to fit your needs.
Our 360° Protection covers:
- Email Threat Protection
- Elite endpoint
- Malware and Ransomware
- Mobile Device
- Cloud Application Security Broker
- Firewall
- SIEM
- Security Operations Center (SOC)
While our solutions are thorough, the ease-of-use on your end is impressive. Ostra will seamlessly integrate with your business, and it dynamically updates so there is no need for you to monitor it. Ostra’s solutions will be hard at work in the background of your system, 24/7.
We’ve made enterprise-grade cybersecurity accessible for all businesses—small or large. By merging our proprietary technology and our strategic partnerships with top cybersecurity solutions out there, we’ve created a unique, cost-effective cybersecurity solution available to businesses of all sizes for the first time.
To get started on incorporating Ostra into your cybersecurity plan, reach out to us today!
As Your Trusted Cybersecurity Team, Ostra makes cybersecurity simple and accessible to businesses of all sizes. Ostra provides its partners and their clients with a multi-layered, comprehensive and fully managed Security as a Service.




